Archive
Pi Approximation Day (yesterday)
Of all the random dates already in my calender, I have just added another! The so called Pi approximation day, which I missed this year, is on the 22nd of July and is so ‘celebrated’ because it mathematically gives a close approximation (divide 22 by 7) to the true value of Pi. Oh well, this time next year (sans one day) I will make a Pi pastry and who knows what else…:)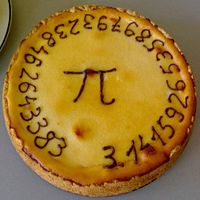
Awesome geekness. Source.
Test your password!
I found a fantastic site today which quickly and transparently tests the strength of your password(s). I would not recommend you actually type your current passwords in (just in case there is some sneaky javascript code) but it is interesting to experiment with different password combinations.
Since I was on the topic of passwords, I ended up writing a brief post about how to choose a good password and general password security.
A good password should be four things:
1) Use at least two cases* (e.g. lower case, upper case, ‘number’ case and ‘character’ case.)
2) Be a suitable length – anything less than 7 characters should be avoided.
3) Not include repetition within the password and should not be used for more than one application.
4) Be something personal or easy to guess (a birthday, pet or family member name or related to the application – for example ’email’ as a password for your email account would be ludicrous.)
Let look at some examples:
The old favourite: “password”. As you can see from the rating below, it is a terrible password. Not only is it predictable (and one of the most commonly used passwords) but it uses only one case and has some repetition (sequential double ‘s’.)

A slightly better version of the old classic: “pa55word”. This time, all I had done is replaced the ‘s’ with the 733t-ified version. By adding numbers, the complexity of the password has increased dramatically although it is still hindered by repetition.

Lets go even further: “Pa55Word”. Now we are using three cases and the result is predictably much stronger than using two cases alone.

And finally, lets go nuts: “Pa5!Word”. Using all the cases available on the Roman alphabet and removing all sequential characters. It is still not a brilliant password, but it is head and shoulders above the others.

Whilst choice and selection of password is important, it is not always essential to pick random strings as your password. Whilst passwords like gY$5c0p[ are very strong (it scored 92%) it is difficult for most people to remember them due to their entropic nature. It is therefore important to marry practicality with security and my advice to anyone picking a password would be to think of a word (or phrase) and substitute some of the letters for numbers / capitals / characters as in the example above**.
Password hints:
1) If you are choosing a very important password, pick a passage from a book. For example, the first 3 (or as many as you want) words from the first line of a particular page** and add a good degree of randomness to it as described above. If you need to jog your memory in the future, simply refer to that page and it should normally come back to you.
2) If you must write or record your password, obfuscate (via a stenographic method) it! Split it in half (or more pieces) and hide the password/passphrase in several bits of innocuous data. For example: If you made your password Nice225 Woods987 then you could store the following contacts somewhere:
William Nice +44207 750 1225
Christian Woods +43133 987 3245
The same method can be applied for card PIN numbers which can be stored as part of a dummy contact on a mobile phone.
3) Never stick to the same password for more than one service – if someone compromises one password, all your services will be vulnerable.
4) Scale your password to the particular security environment. A password that is used for an unencrypted email account need not be as strong as one for a SSH / VPN / Remote Terminal or VNC account.
5) For accounts you are particularly cautions with, rotate your password frequently. This need not be very week or even every month. If you change your password every 2 or 3 months, it will provide a much better protection against online stalkers who may be lurking and checking your accounts / emails periodically.
6) Passwords can be passphrases! It is much easier to remember a line of a story / poem etc than a bunch of rubbish. Unfortunately, even if that line of text is long enough, it will not offset the problems** caused by character repetition, although it would be important to obfuscate it in some way.
Appendix
* The reason cases are so important is simply a matter of maths. If an attacker knows the password is only one (or two) cases, it significantly reduces the amount of computational time to brute force (or guess) the password. Take for example, a password with only one case (lets assume its lower case). There are only, 26 characters in the Western (Roman) alphabet meaning the complexity of the password is:
…if the password is 4 characters long, there are : 456976 combinations.
If the password is 8 characters long, there are : 208827064576 combinations.
Now lets assume two cases (lower and upper case) are used. Now the attacker has to try a total of 52 character combinations for every character suspected to be in the password.
…if the password is 4 characters long, there are : 7311616 combinations.
If the password is 8 characters long, there are : 53459728531456 combinations.
You can quickly see the significance in the numbers. If to round it off, we try all the (printable) characters available (94), an 8 character long password would have 6095689385410816 combinations!!
** Generally speaking, when trying to create a password, we are trying to create as entropic an outcome as possible as this will be the most computationally time consuming to break. The entropic value measured per key is calculated on the basis that each key press is independent and the entropy per key essentially increases with increased character range.

1 Source
2 Source
Due to the manner in which language is constructed, the occurrence of letter like vowels is dramatically increased leading to a much decreased entropy per key. This means, in order to create a reasonable secure 64bit key, you would need approximately 58 characters as opposed to only 10 if all characters are used.e
